# Example Role centric PEP
## Role centric Enforcement Point
### Use case example
We want to define a policy to restrict access to the Soffid console role's page (MainMenu > Administration > Resources > Roles).
The users who belong to the "enterprise" group as primary group (from this point forward: *end-users*) will have limitations to perform some actions on the Soffid console roles page.
1. The *end-users* could query all the roles information.
2. The *end-users* could update any role in the information systems "ERP RRHH"
3. The *end-users* could not create any role.
4. The *end-users* could not delete any role.
### XACML Editor
#### Policy set
First of all, we define a policy set. We need to define the subject, in that case users who belong to "enterprise" as primary group.
[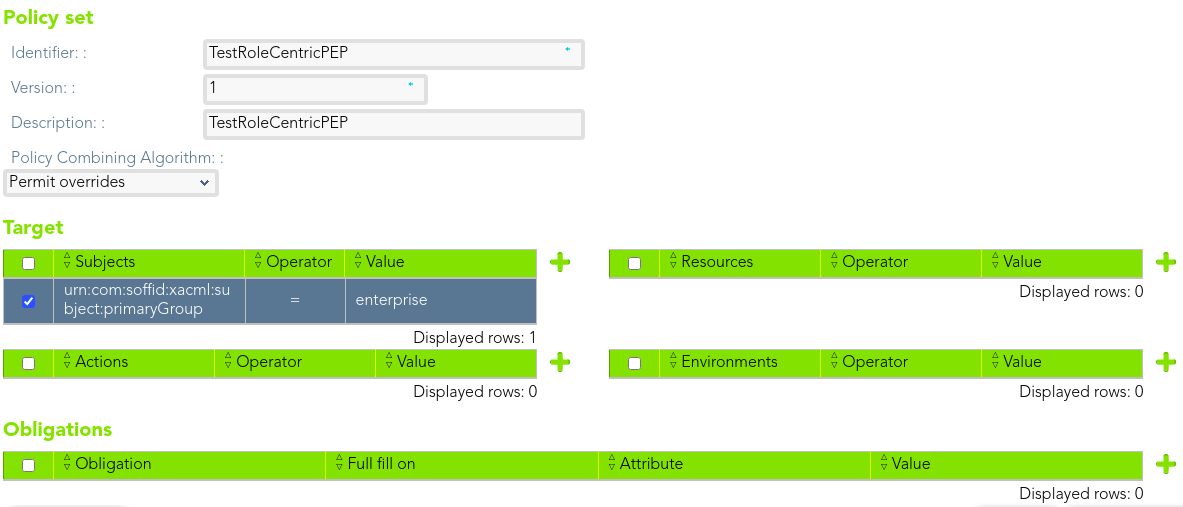](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238451051.png)
Then, we can define a policy to manage the different actions that the *end-users* could perform.
[](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238488177.png)
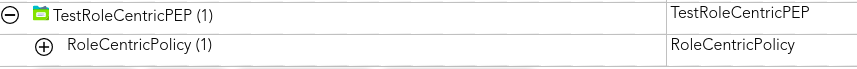
#### Policy
The policy will apply to an only one user. That policy will be to protect the role resource.
[](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238516436.png)
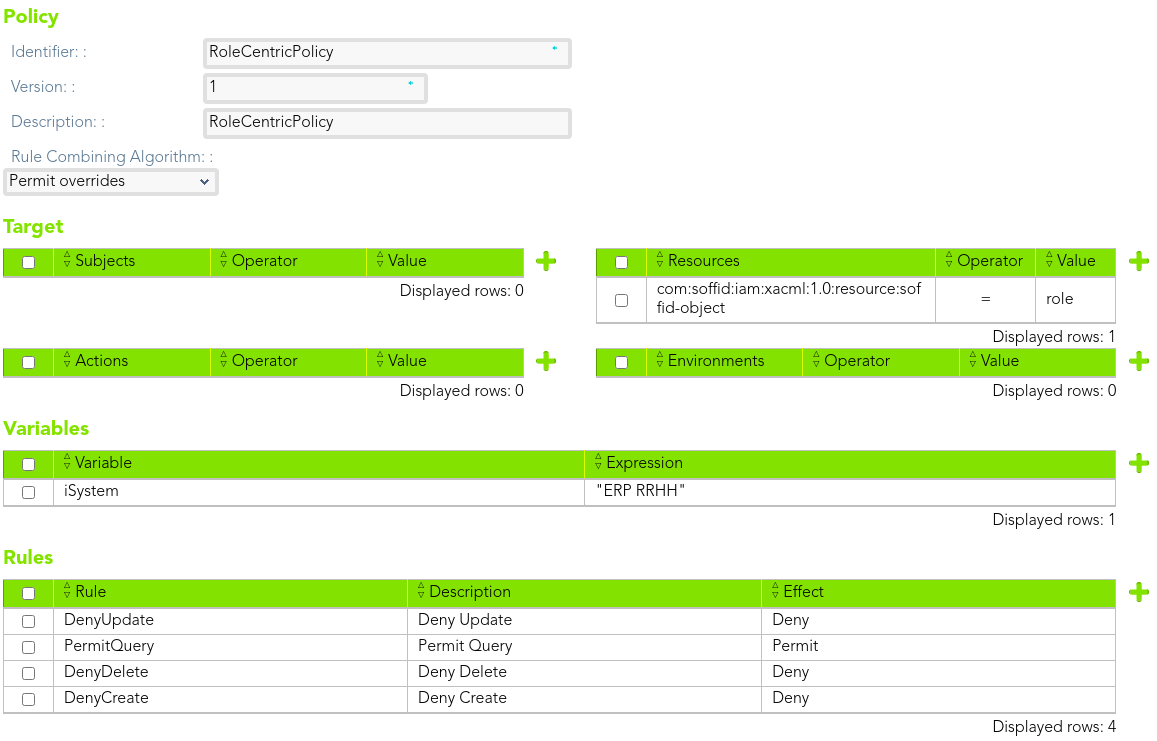
##### Rule 1
> The *end-users* could query all the roles information.
We define the rule that allow to the end-users to query all the roles information.
[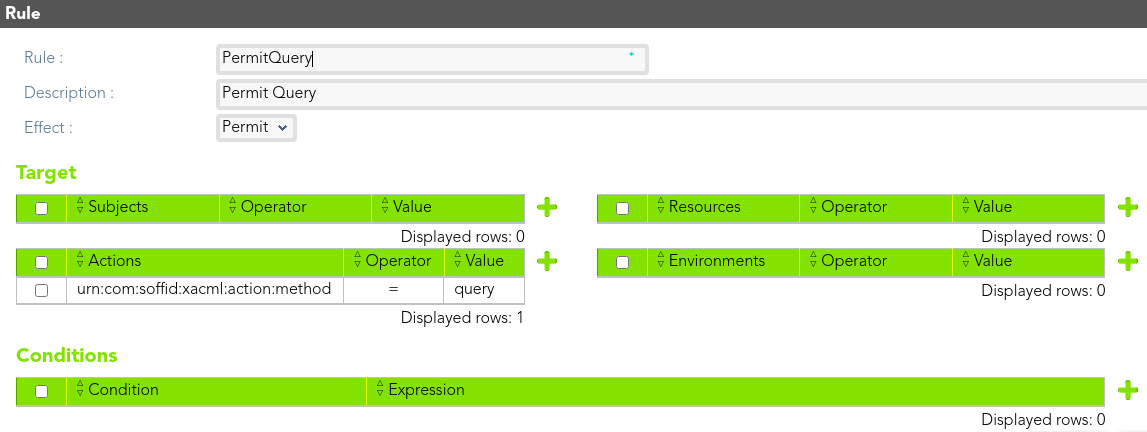](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238550714.png)
##### Rule 2
> The *end-users* could update any role in the information systems "ERP RRHH"
[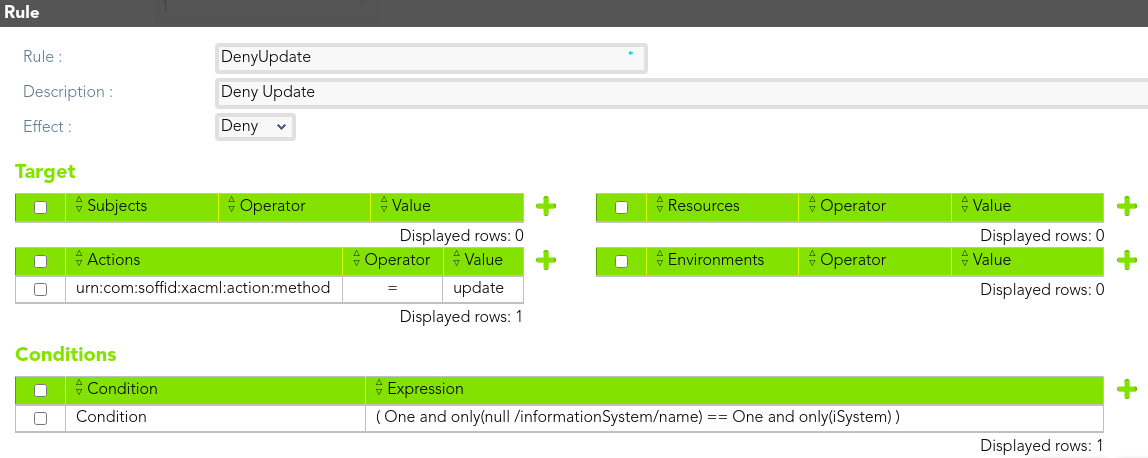](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238577406.png)
##### Rule 3
> The *end-users* could not create any role.
[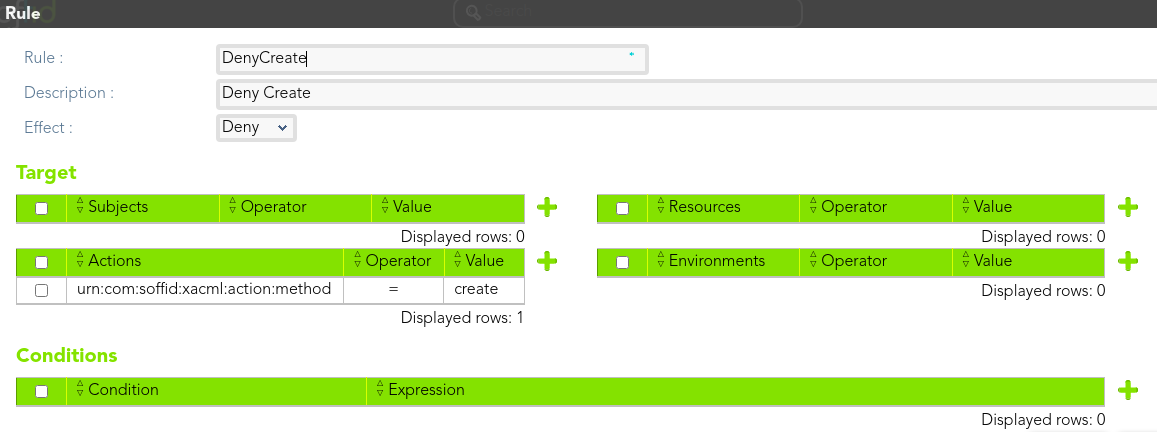](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238610498.png)
##### Rule 4
> The *end-users* could not delete any role.
[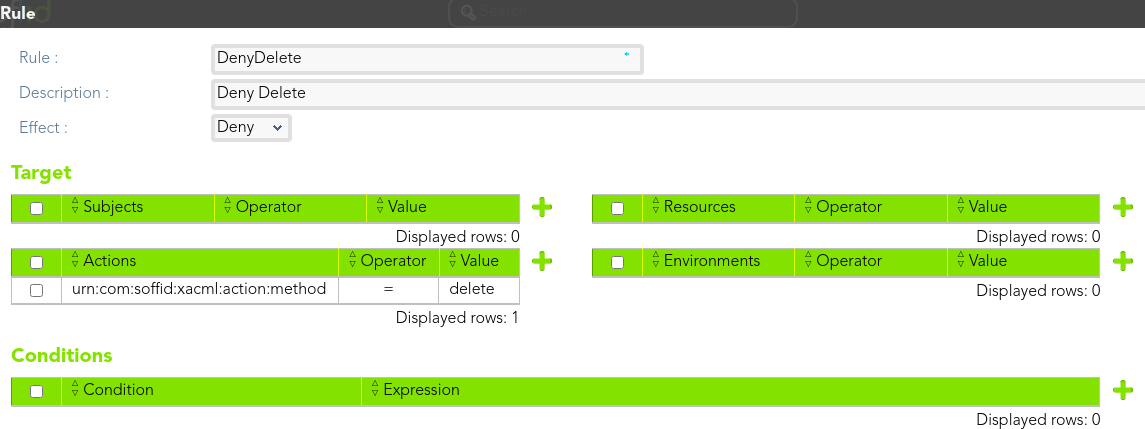](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238769335.png)
### Download XML
You can download a XML file with the example: [policy-TestRoleCentricPEP.xml](https://bookstack.soffid.com/attachments/21)
## Configure PEP
[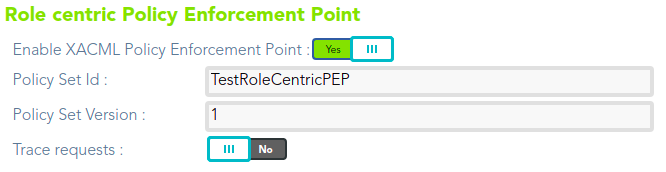](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238733004.png)