You can download a XML file with the example: [policy-TestWebPEP.xml](https://bookstack.soffid.com/attachments/22)
## Configure PEP [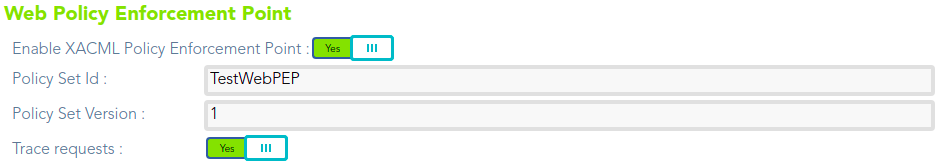](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628235091281.png) # Example Role centric PEP ## Role centric Enforcement Point ### Use case example We want to define a policy to restrict access to the Soffid console role's page ( > Administration > Resources > Roles). The users who belong to the "enterprise" group as primary group (from this point forward: *end-users*) will have limitations to perform some actions on the Soffid console roles page. 1. The *end-users* could query all the roles information. 2. The *end-users* could update any role in the information systems "ERP RRHH" 3. The *end-users* could not create any role. 4. The *end-users* could not delete any role. ### XACML Editor #### Policy set First of all, we define a policy set. We need to define the subject, in that case users who belong to "enterprise" as primary group. [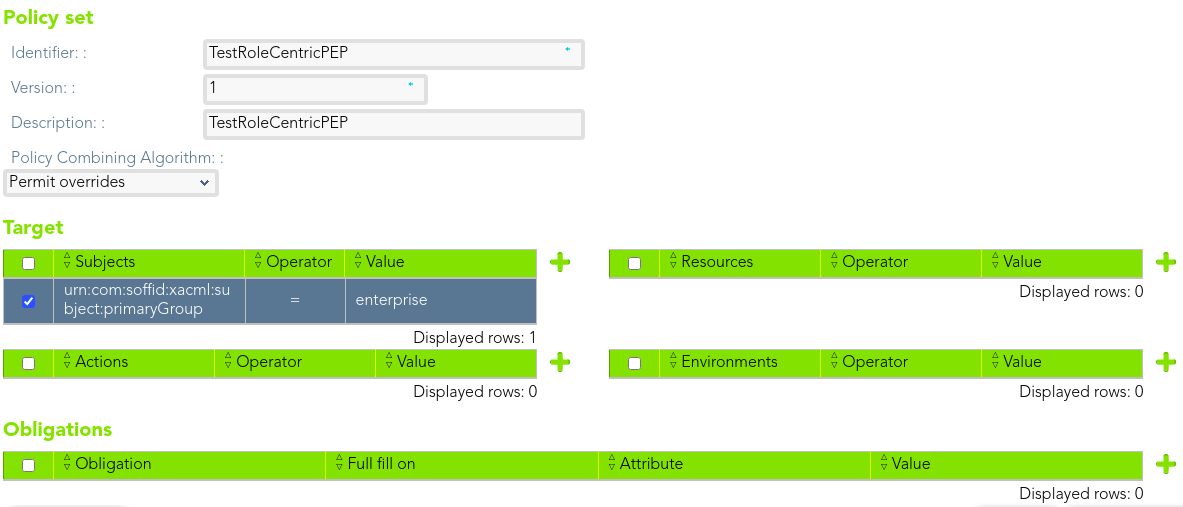](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238451051.png) Then, we can define a policy to manage the different actions that the *end-users* could perform. [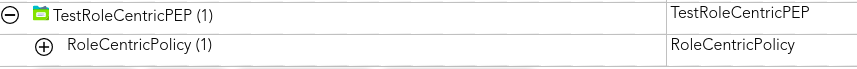](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238488177.png) #### Policy The policy will apply to an only one user. That policy will be to protect the role resource. [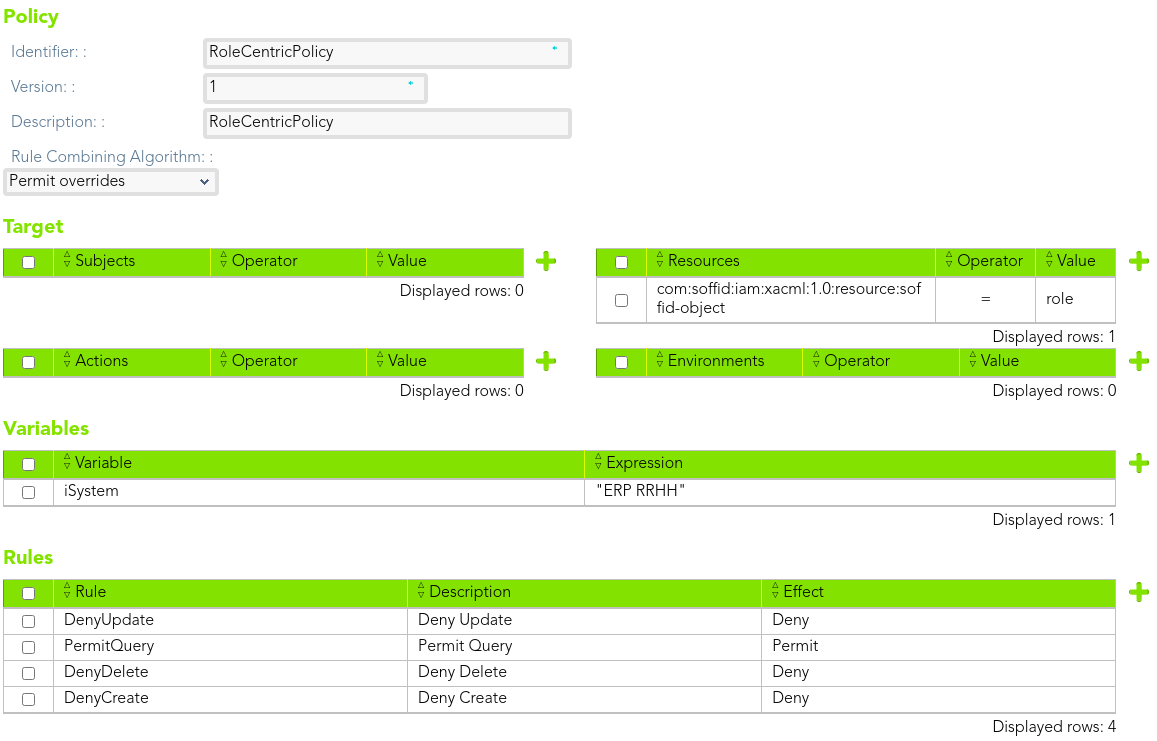](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238516436.png) ##### Rule 1 > The *end-users* could query all the roles information. We define the rule that allow to the end-users to query all the roles information. [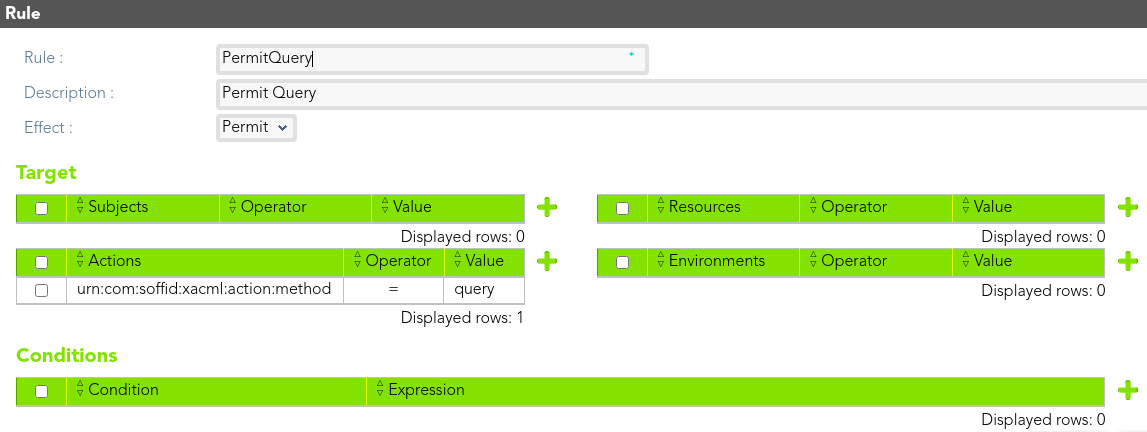](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238550714.png) ##### Rule 2 > The *end-users* could update any role in the information systems "ERP RRHH" [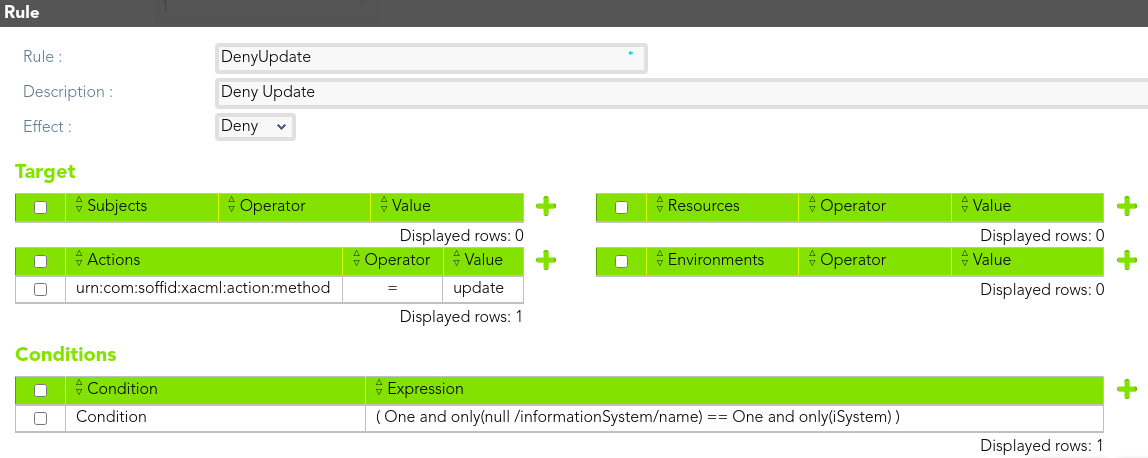](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238577406.png) ##### Rule 3 > The *end-users* could not create any role. [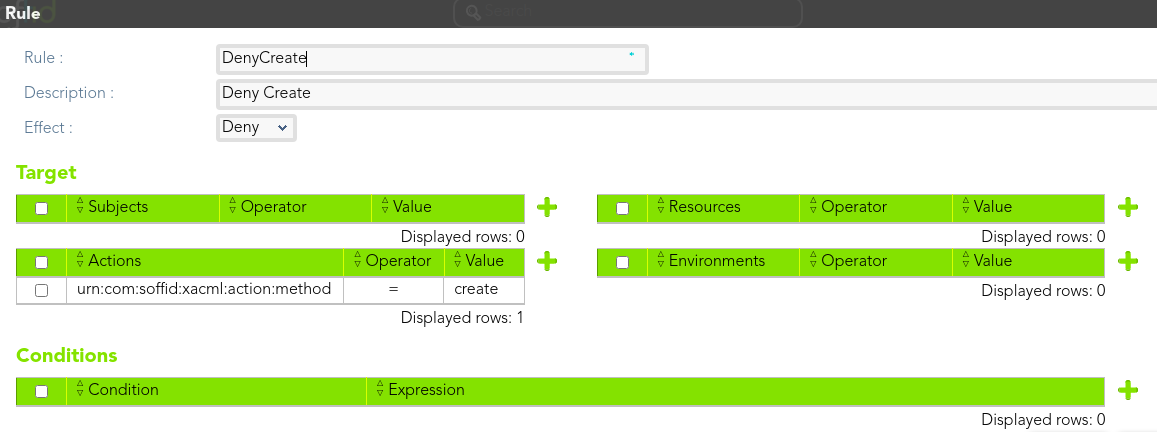](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238610498.png) ##### Rule 4 > The *end-users* could not delete any role. [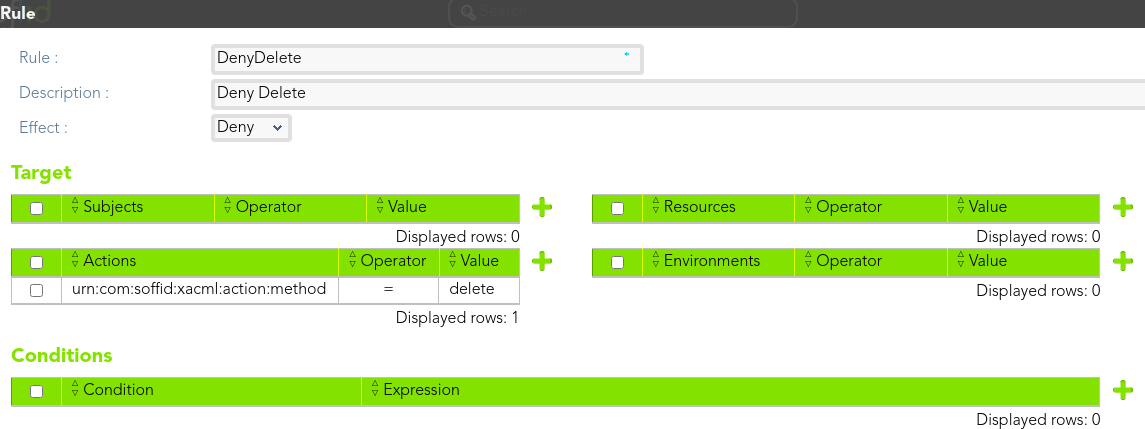](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238769335.png) ### Download XMLYou can download a XML file with the example: [policy-TestRoleCentricPEP.xml](https://bookstack.soffid.com/attachments/21)
## Configure PEP [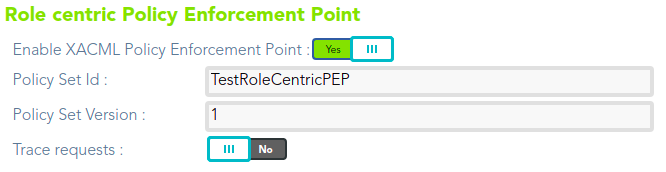](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238733004.png) # Example Dynamic role PEP ## Dynamic role Enforcement Point ### Use case example We want to define a policy to restrict access to the Soffid console user's page ( > Administration > Resources > Users). The users who are assigned to the SOFFID\_RRHH role (from this point forward: *end-users*) will have limitations to perform some actions on the Soffid console users page: 1. The *end-users* only be able to query the information about the users who belong to the same primary group that them. 2. The *end-users* only be able to update the users with internal user type. 3. The *end-users* could not delete any user record. ### XACML Editor #### Policy set First of all, we define a policy set. We need to define the subject, in that case users with SOFFID\_RRHH role assigned. [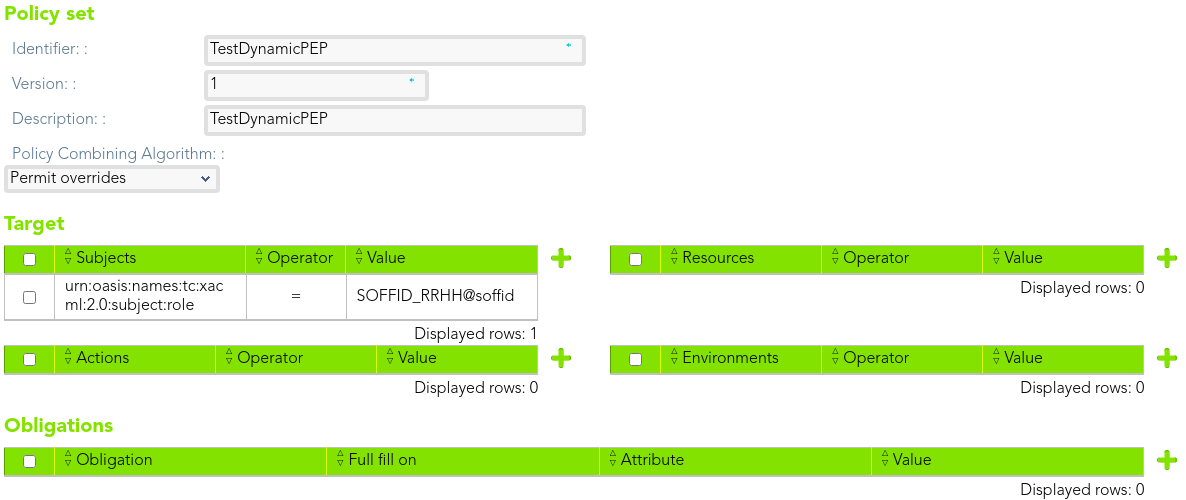](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628231702828.png) Then, we can create the policies, in that case, we can create three policies, one for each operation that we want to manage. [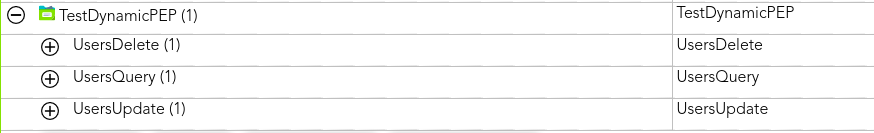](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238915331.png) #### Policies We can define a policy for each operation, to permit or deny access. Also, we can define a variable that contains the *end-user* primary group in order to use it when we define the conditions. ##### Policy1 > The *end-users* only be able to query the information about the users who belong to the same primary group that them. We need to define two rules, one to permit and other to deny access. [](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238946431.png) ##### Rules We define the rule that allow to the *end-user* to query users information who belong to the same primary group that the end-user. [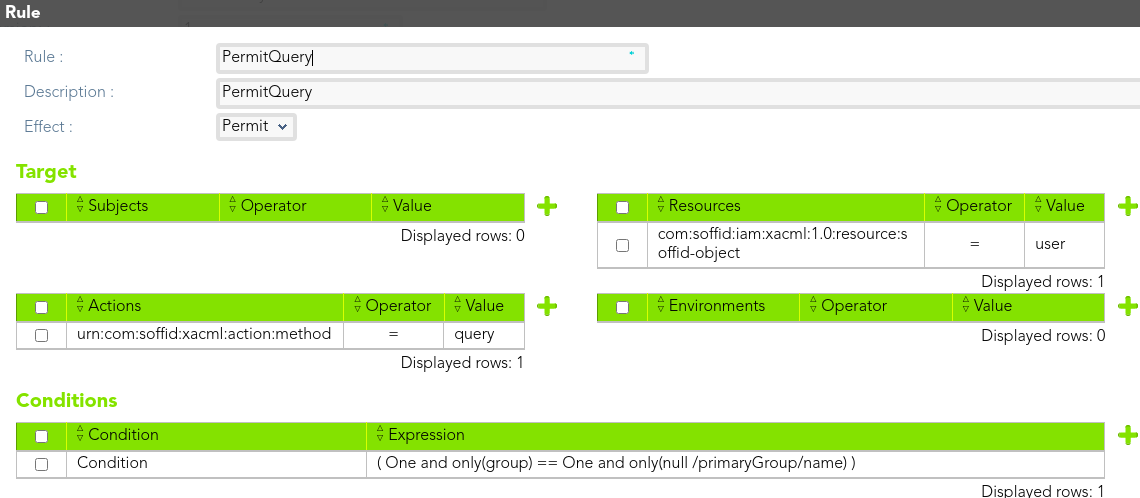](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238975450.png) Then, we define the rule that denies access to *end-users* to query users information. [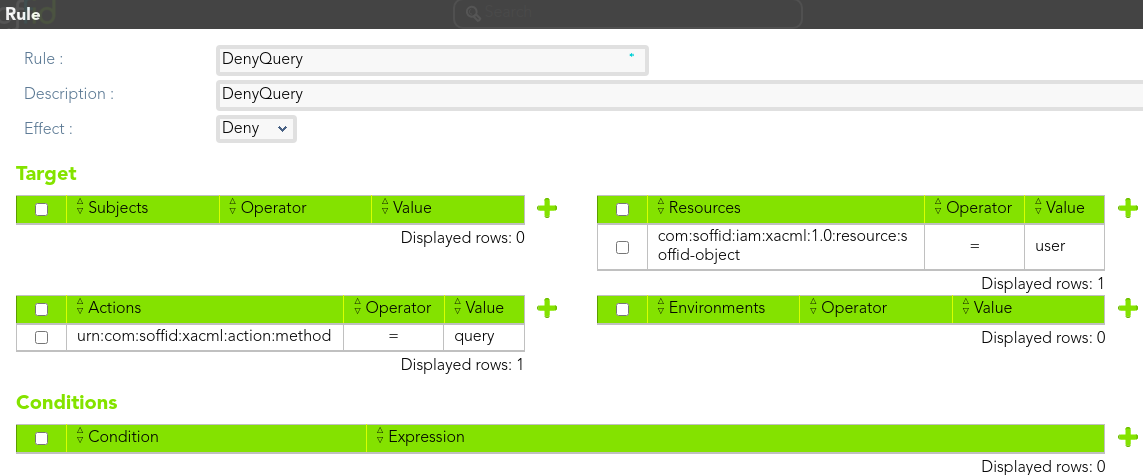](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239000393.png) ##### Policy 2 > The *end-users* only be able to update the users with internal user type. We need to define two rules, one to permit and other to deny access. [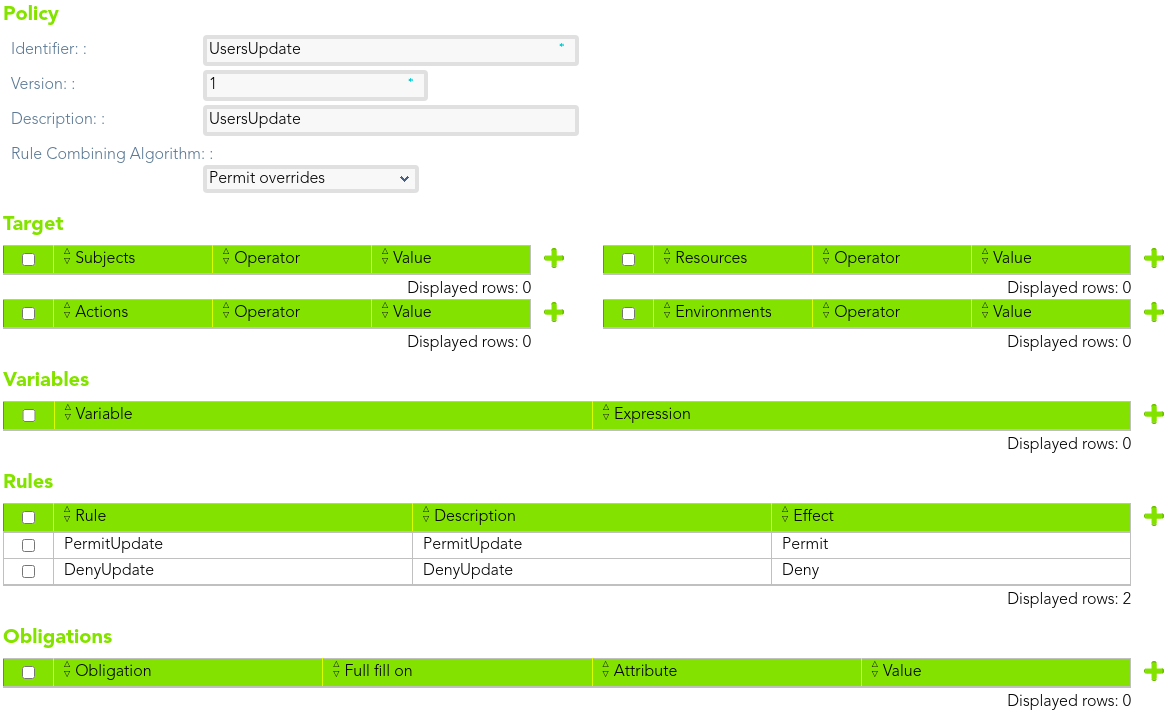](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239036221.png) ##### Rules We define the rule that allow to the *end-users to* update users information who are internal users. [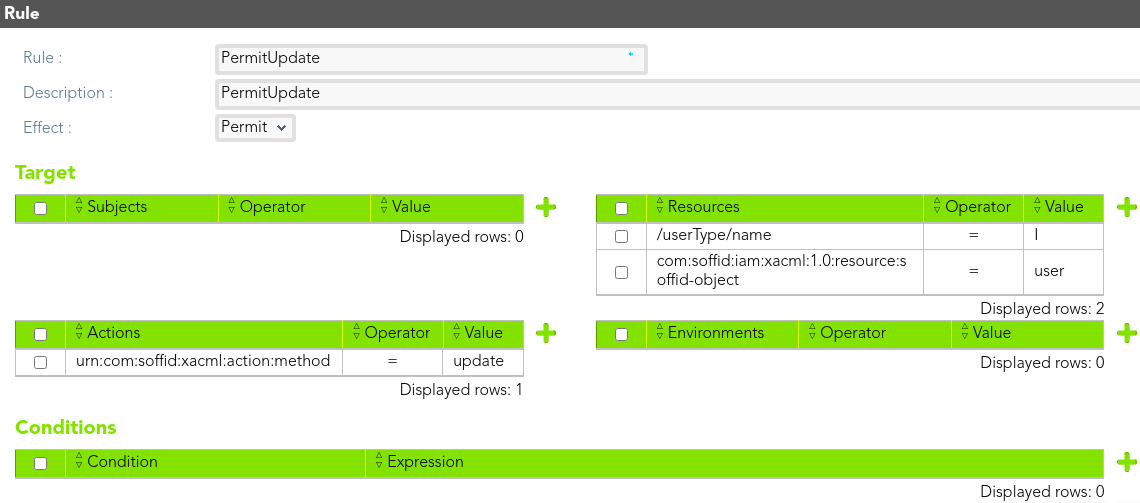](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239076738.png) Then, we define the rule that denies access to *end-users* to update users information. [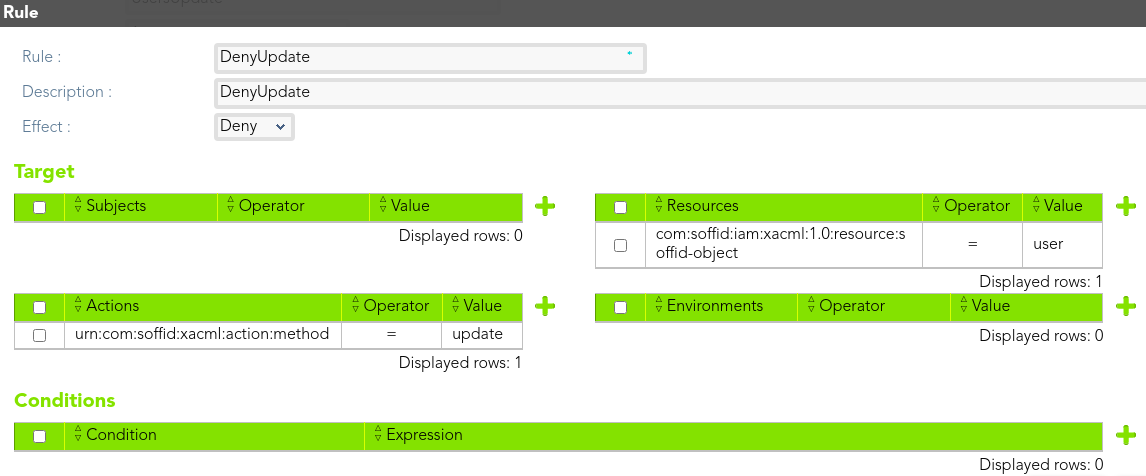](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239102464.png) ##### Policy 3 > The *end-users* could not delete any user record. We need to define only one rule to deny access. [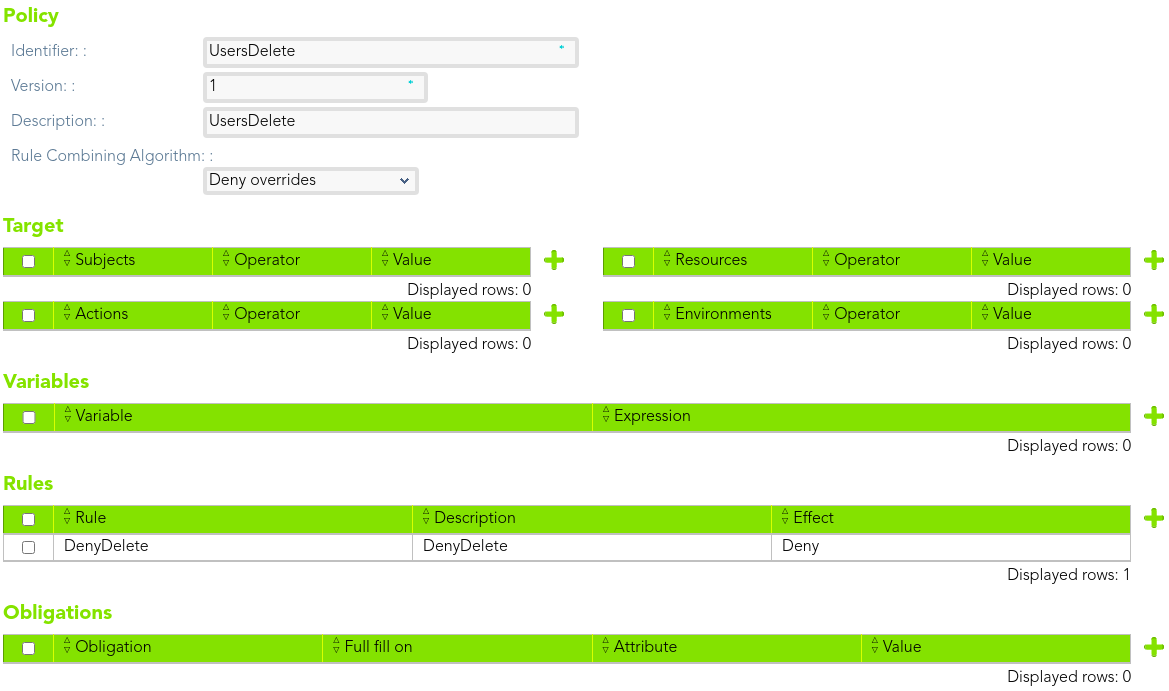](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239130798.png) ##### Rules We define the rule that deny to the *end-user* delete any user. [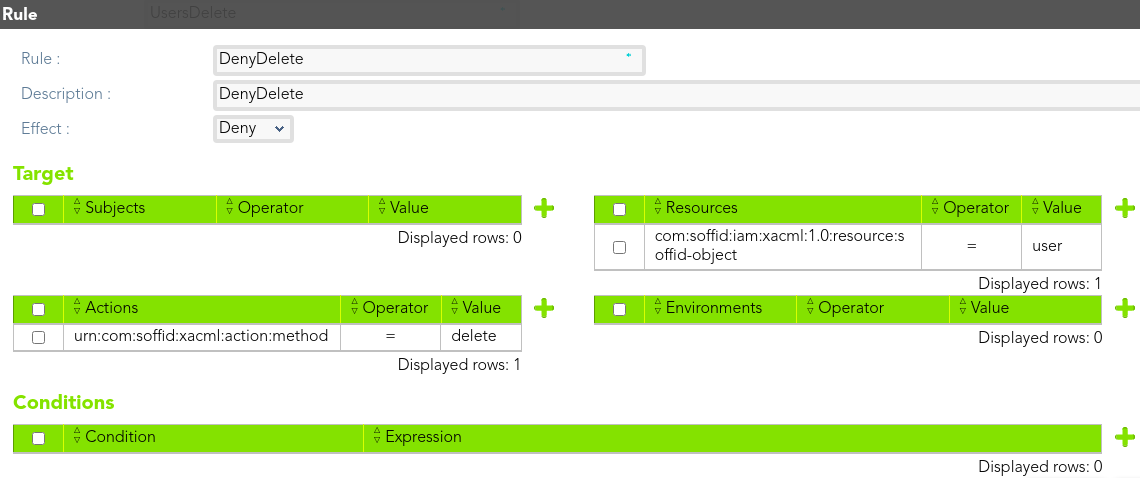](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239173903.png) ### Download XMLYou can download a XML file with the example: [policy-TestDynamicPEP.xml](https://bookstack.soffid.com/attachments/20)
## Configure PEP [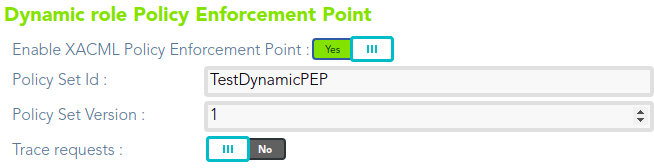](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628238841651.png) # Example Password Vault PEP ## Password Vault Policy Enforcement Point ### Use case example 1 We want to define a policy to restrict access to the Soffid Password Vault. The users who are assigned to the SOFFID\_ADMIN role (from this point forward: end-users) will have limitations to perform some actions on the folder "demoFolder" of the Soffid Password Vault 1. The end-users only be able to access the accounts of that folder on labor time. The permissions will be denied in another case. ### Policy set First of all, we define a policy set that could contain other policy sets and policies. [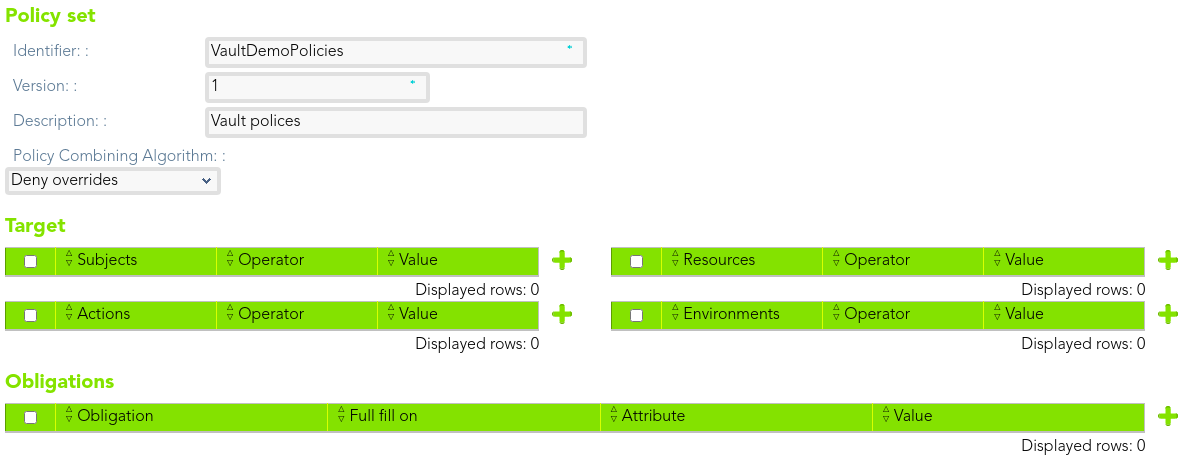](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628240486192.png) ### Policy set 2 Then, we can create another policy set as a child of the former to manage the folder and to define the subject, in that case, users with SOFFID\_ADMIN role assigned. [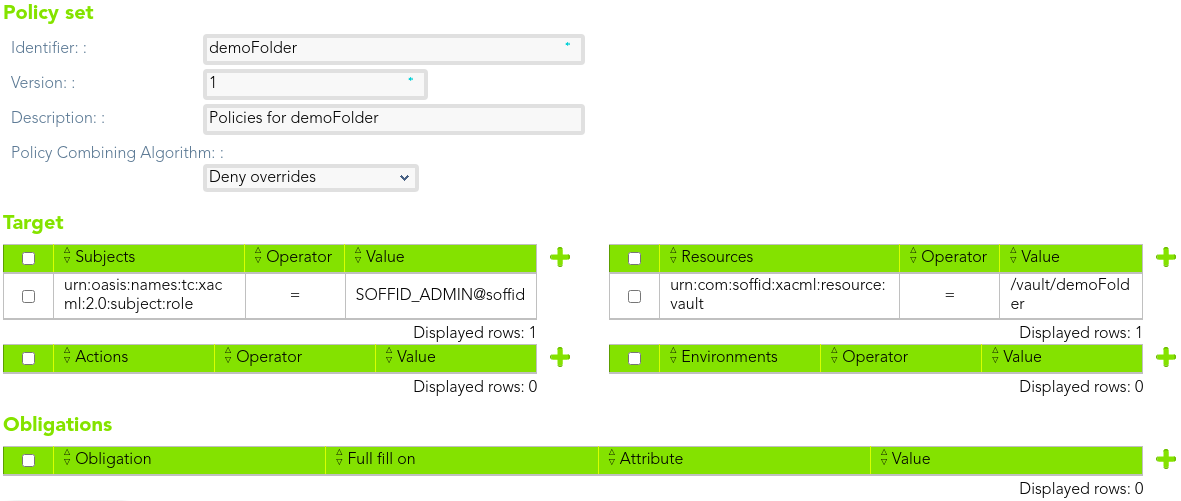](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628240781296.png) That policy set will contain the policies. [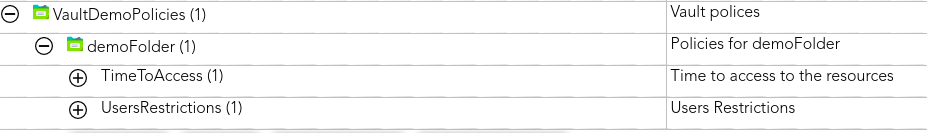](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628240820879.png) ### Policies #### Policy 1 > The end-users only be able to access the accounts of that folder on labour time. The permissions will be denied in other case. [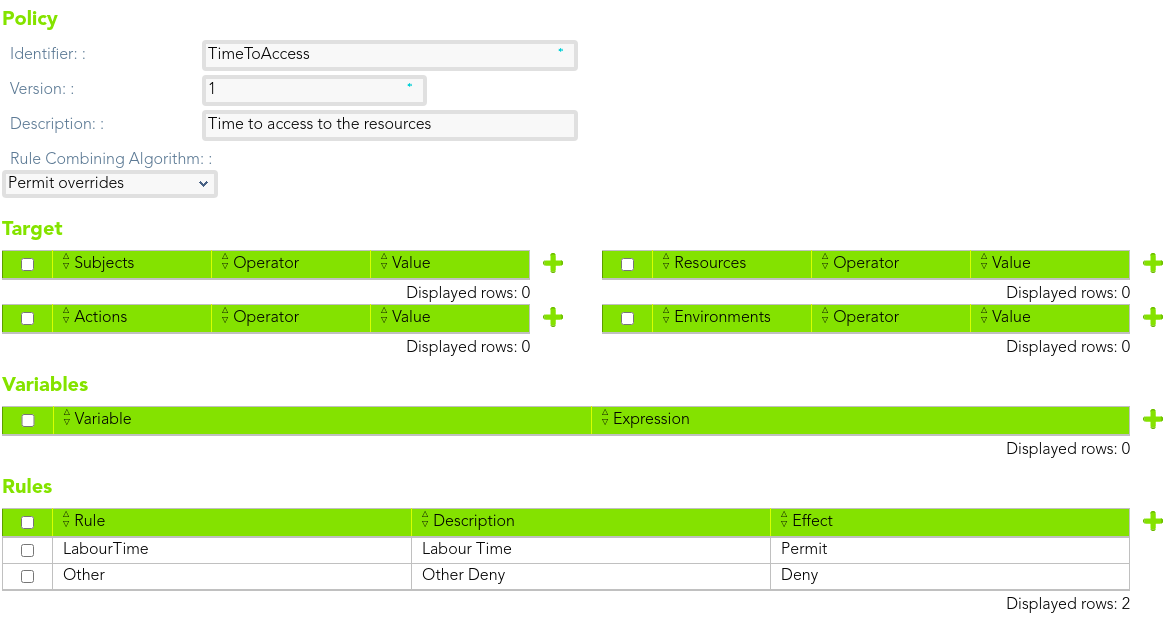](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628240889871.png) ##### Rule We define the rule that permit access to the *end-user* [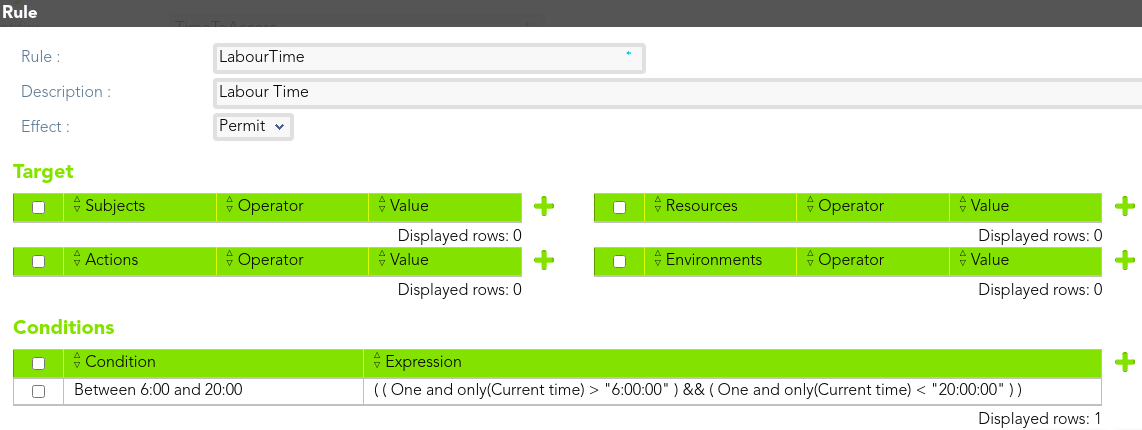](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628241172154.png) And we define other to deny access. [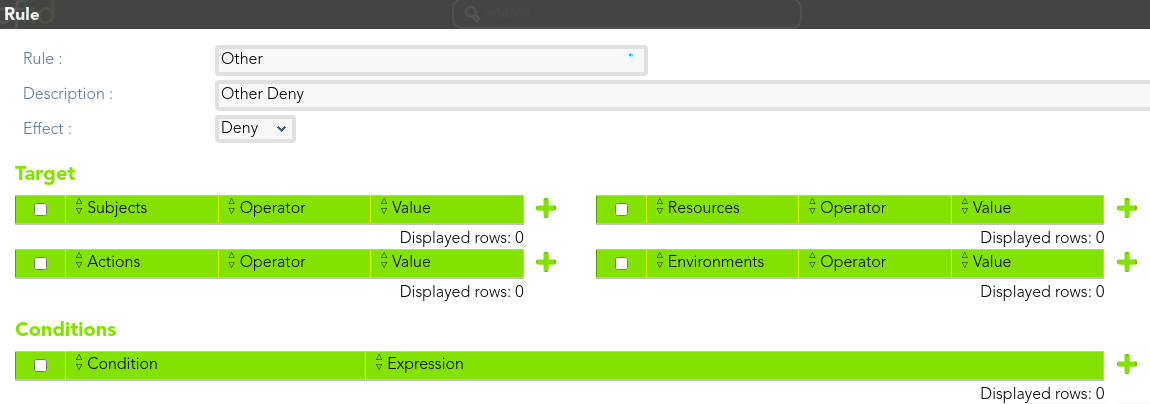](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628241209362.png) ### Use case example 2 We want to define a policy to restrict access to the Soffid Password Vault. The users who are assigned to the SOFFID\_ADMIN role (from this point forward: end-users) will have limitations to perform some actions on the folder "demoFolder" of the Soffid Password Vault 1. The end-users only be able to access the accounts of that folder on labor time. The permissions will be denied in another case. (Use case example 1) 2. To connect there are some obligations to fulfill [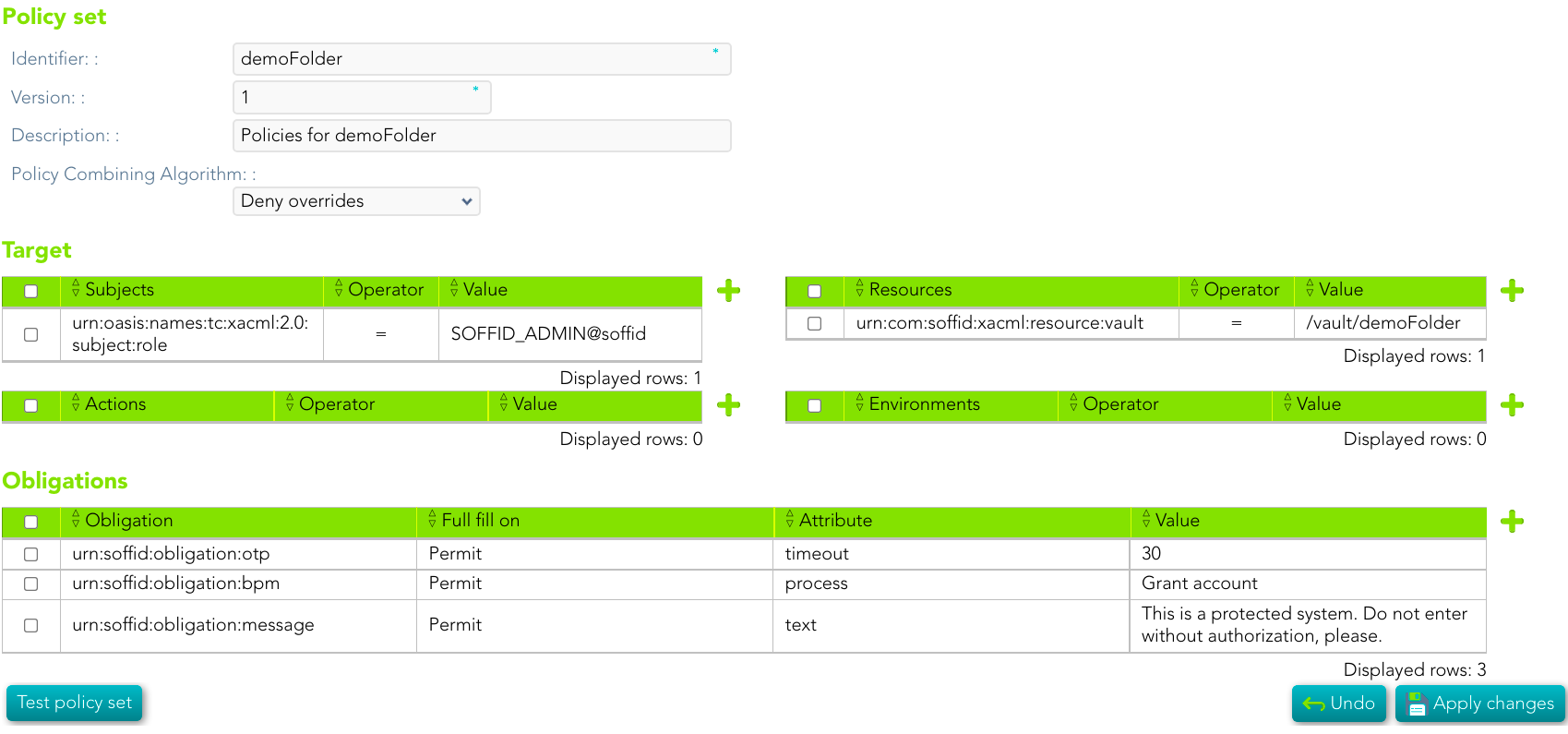](https://bookstack.soffid.com/uploads/images/gallery/2022-02/image-1643698970894.png) ### Use case example 3 We want to define a policy to restrict access to the Soffid Password Vault. The access will be denied on Sunday. [](https://bookstack.soffid.com/uploads/images/gallery/2023-09/image-1695648483304.png) ### Download XMLYou can download an XML file with the example: [policy-demoFolder.xml](https://bookstack.soffid.com/attachments/23)
## Configure PEP [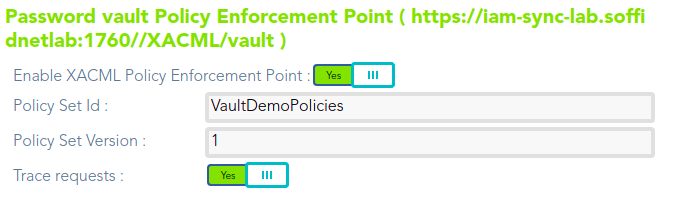](https://bookstack.soffid.com/uploads/images/gallery/2021-08/image-1628239716307.png)