You can follow the defined steps in the [PAM Install & config book](https://bookstack.soffid.com/books/pam-install-config "PAM Install & config").
## Deployment procedure ### 1. Networks `Main Menu > Administration > Resources > Networks` You need to add your company networks or the networks you want to manage, on Soffid Console. To do that you need to create those networks on the Networks page. Once you have created your networks, you could continue with the next step.You can find more information on the [Networks page](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/networks "Networks").
### 2. Config Network discovery `Main Menu > Administration > Resources > Network discovery` When you open the Network discovery page, Soffid will display all the networks create on Soffid Console. The network discovery process can be launched for each network, to do that, you need to configure the potential administrator accounts to connect to the hosts for each network. You can add one or more potential administrator accounts to try to connect to the network hosts. These can be new accounts or existing accounts on Soffid. Also, you can remove accounts from the accounts to probe list. If you remove an account from the list, that account will continue to exist on Soffid.You can find more information on the [Network discovery page](https://bookstack.soffid.com/books/pam-deployment/page/network-discovery "Network discovery").
Once you have configured the Network discovery parameter for a network, you could execute the process to begin to search or you could schedule the process execution. ### 3. Launch Network discovery `Main Menu > Administration > Resources > Network discovery` The Network discovery process is an unattended process. You could launch it, and it will be working until it will finish, even you close your Soffid session. The Network discovery process could be a long process, depending on the network size, the number of hosts, and the firewalls as well.You can find more information on the [Network discovery page](https://bookstack.soffid.com/books/pam-deployment/page/network-discovery "Network discovery").
#### 3.1. Agent definition When the network discovery process is launched, as the process finds hosts, it will try to connect to them using the defined credentials. When it gets to connect to the host with one credential, it will not try again with others. If it gets to connect to the host, it will create automatically a Soffid agent with the proper attributes and connector parameters, also with the necessary account metadata. #### 3.2. Accounts / Account protected services Then, the reconciliation process of the created agent will be launched and it will try to recover the information about the accounts defined on the host. Also, it will try to recover the information about the account protected services. #### 3.4. Entry points The Network discovery process will create, in possible cases, a new entry point to the host with the basic attributes, and the proper executions to run it. That entry point will display on the Application access tree page. ### 4. Password vault `Main Menu > Administration > Resources > Password vault` When the network discovery process finishes, it will be really important to determine what are the critical accounts. Those critical accounts should be located in protected storage, the Password vault. On the password vault, you can locate the accounts, especially the critical account used to access critical systems. Password vault allows you to handle the access control list to these accounts, here you can define who are the owners, the managers, and the SSO users. You need to configure in the right way the control access list, to allow only the proper users to change and view the passwords.You can find more information on the[ Password vault page.](https://bookstack.soffid.com/books/pam-deployment/page/password-vault "Password vault")
### 5. Authorization processes Soffid allows you to define and add approval processes to manage the use of critical accounts, where the manager or authorized user will approve or deny using them. To define and configure approval workflows, you can use the Soffid BPM editor `Main Menu > Administration > Configure Soffid > Workflow settings > BPM editor`You can visit the[ BPM Editor book](https://bookstack.soffid.com/books/bpm-editor "BPM Editor") to find more information.
One you have defined the approval process, you need to establish the relationship between the workflow and the account or accounts, to do that you need to configure the XACML Policy Management and the XACML PEP configuration. ### 6. XACMLFor detailed information about XACML, you can visit the [XACML book](https://bookstack.soffid.com/books/xacml "XACML").
#### 6.1. XACML Policy Management Using XACML Soffid can be able to add more complex and restricted rules to the authorizations. Here you can define policy sets and policies to describe general access control requirements. Also, you can define some obligations as actions that have to be returned with response XACML. Here you can indicate the use of an authorization process. `Main Menu > Administration > Configure Soffid > Security settings > XACML Policy Management` #### 6.2. XACML PEP configuration You will need to enable and configure the Password vault Policy Enforcement Point (PEP). That is the way that Soffid provides to establish the relationship between the Authorization processes and the Password vault. Be in mind, you only can configure one Password vault PEP, the policy set that you define, can contain more policy sets and policies to cover all your company needs. `Main Menu > Administration > Configure Soffid > Security settings > XACML PEP configuration` ### 7. PAM policies and PAM rules Using PAM all the sessions will be recorded (Screen, KeyBoard, Clipboard, and File transfers). Soffid allows you to configure policies based on rules, so when each one of the rules is fulfilled, one or more actions will be triggered according to the configuration. The available actions are to close the session, lock the account, open an issue on a ticketing system and notify the breaking rule. You can find more information visiting the and the. #### 7.1. PAM rules `Main Menu > Administration > Configure Soffid > Security settings > PAM rules` You can define rules to detect commands executed on a server. When a user launches a command defined on a rule, Soffid will detect it.For detailed information about PAM Rules, you can visit the [PAM Rules page.](https://bookstack.soffid.com/books/configure-pam/page/pam-rules "PAM Rules")
#### 7.2. PAM policies `Main Menu > Administration > Configure Soffid > Security settings > PAM policies` You can define policies made up of several rules. For each rule, you could select the action to perform when Soffid detects that rule is accomplished. On the Password Vault page, you can assign a PAM policy to each folder, depending on your needs.For detailed information about PAM Policies, you can visit the [PAM Policies page](https://bookstack.soffid.com/books/configure-pam/page/pam-policies "PAM Policies").
--- (\*) [https://en.wikipedia.org/wiki/Jump\_server](https://en.wikipedia.org/wiki/Jump_server) # Configuration # Network discovery ## Description The Network discovery tool will be in charge to scan the networks to find the hosts and retrieve information about user accounts. Network discovery can detect system accounts as well. First of all, you need to create the networks that you want to scan. Visit the [Networks page](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/networks "Networks") for more information. Then, on the Network discovery page, you need to configure for each network, the accounts and passwords of potential administrators to connect to the host and retrieve the information. And finally, you need to start the process execution or you can schedule the execution of the network discovery task. The operating system of machines can be Windows or Linux and it is not necessary to install any additional software on those machines.When the Network discovery process is finished, it is **recommended to launch the Reconciliation process of the agents** created by the process to detect the **Account protected services.** To know how to run the Renconciliation process you can visit [the Agents page](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/agents).
Once the machines and accounts, both user and system, have been discovered, the critical accounts must be located in the password vault. You can visit the [Password vault page](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/password-vault "Password vault") for more information.
### How Network discovery works? The **Network Discovery** is the tool in charge to scan the network to discover the hosts of the network. For each host discovered, the **Nmap** utility gets the info about the ports and the protocols used. Also, that process gets the IP Address and the operating system. All the recover information will be saved on Soffid database. The discovery proxy server works as a proxy to connect to the target systems. When the discovery manager discovers a host, it gets the host information and then, through discovery proxy server, it attempts to connect to the host using the accounts defined on the accounts to probe list. - If it can not connect to the host, it will attempt with the next host discovered. - If it gets to connect to the host, then it will create automatically a Soffid agent with the proper attributes and connector parameters, also with the necessary account metadata. Then, the reconciliation process of the created agent, will be launched and it will try to recover the information about the accounts defined on the host. Also, it will try to recover the information about the account protected services. The recover information will be saved on Soffid database. ## Screen overview ## Standard attributes ### Network attributes #### Basic Those attributes are readOnly, you can update them on the [Networks page](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/networks "Networks"). - **Name**: network name. - **Description**: a brief description. - **IP Address**: IP range of this network. - **IP address mask**: IP mask of this network. - **IP ranges to analyze**: allows you to set the range of IPs to scanIt may be necessary to perform the **Reconciliation process of the proper agent** in order to obtain the information from the Account protected services
| **Add new account repository** | Allows you to create a new agent.
You must select the System type and the login name and password. When the agent is created, if the connection is successful, the reconciliation process will be executed.
💻 Image[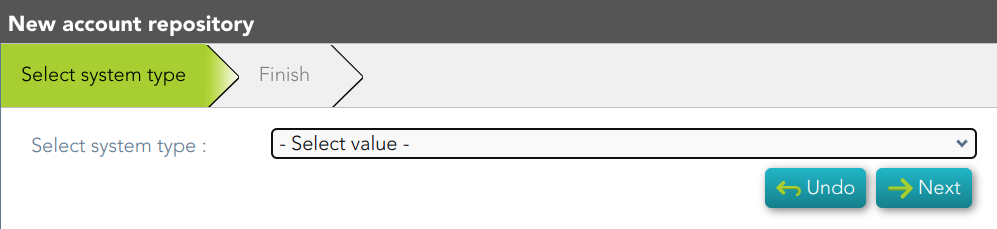](https://bookstack.soffid.com/uploads/images/gallery/2023-12/image-1701426264500.png) |
| **Agent definition** | Allows you to browse to the agent definition. |
| **Accounts** | Allows you to browse the accounts page and the accounts, which belong to this system, will be displayed |
| **Add new entry point** | Allows you to create a new entry point.
You must select the Entry point type and the pale to locate it. Once the entry point is created, you can connect to the target system. Bear in mind, that if you need to create an account to connect, when you set the password to this account, the system (agent) must be in No ReadOnly mode.
💻 Image[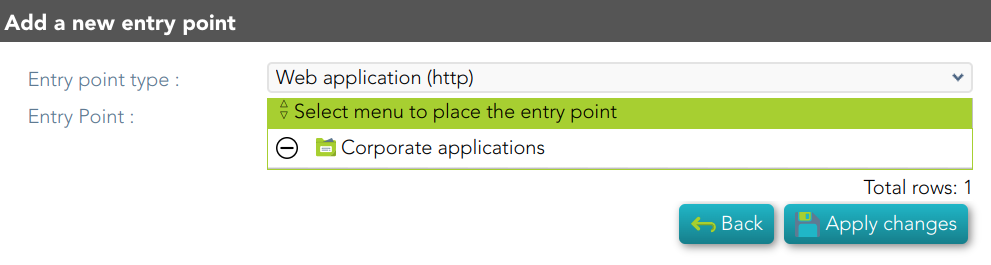](https://bookstack.soffid.com/uploads/images/gallery/2023-12/image-1701426470540.png) |
| **Entry point definition** | Allows you to browse to the entry point definition. |
| **Apply changes** | Allows you to save the data of network detail. To save the data it will be mandatory to fill in the required fields. |
| **Undo** | Allows you to undo any changes made. |
| **Add** | Allows you to add a new administrator potential account to connect to the machines of the network. To add a new account, first of all, you need to click the add button (+) and close the accounts to probe list. Then you will need to choose if you want to add an existing account or register a new account. save the data of a new network or update the data of a specific network. To save the data it will be mandatory to fill in the required fields |
| **Delete** | Allows you to delete one or more accounts of the accounts to probe. You need to select one or more records and next click the button with the subtraction symbol (-). |
| **Start now** | Allows you to launch the task execution. |
| **Logs** | Allows you to download the log files of previous executions. |
| **Delete** | Allows you to delete the machine and the PAM connectors for the device. Soffid will display a message to confirm the deletion process. |
Soffid allows you to define rules to detect commands executed on a server. When a user launches a command defined on a rule, Soffid will detect it.
To use those rules you need to define the PAM policies. For more information, you can visit the [PAM policies page.](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/password-policies "Password policies") ## Screen overview [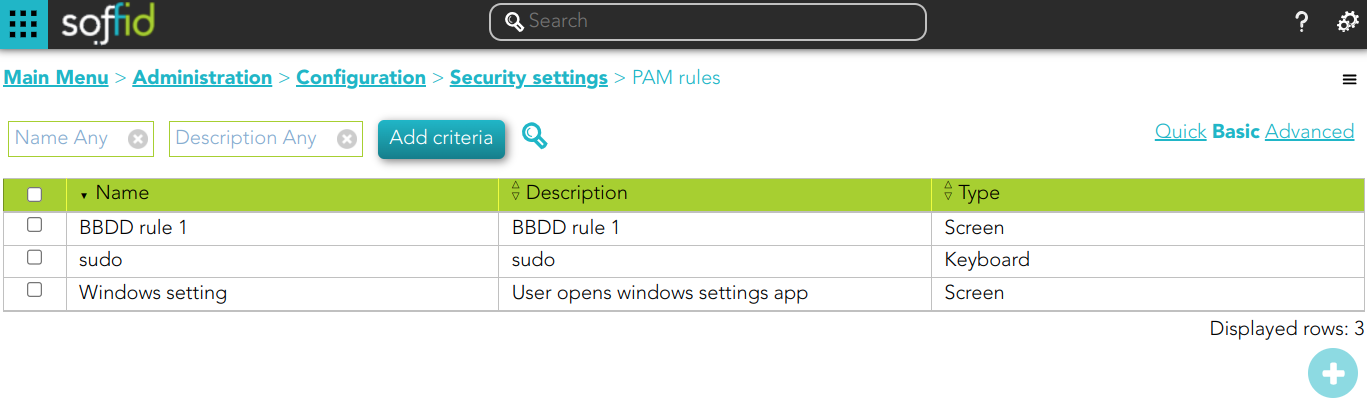](https://bookstack.soffid.com/uploads/images/gallery/2023-10/image-1696499283030.png) ##### Keyboard example [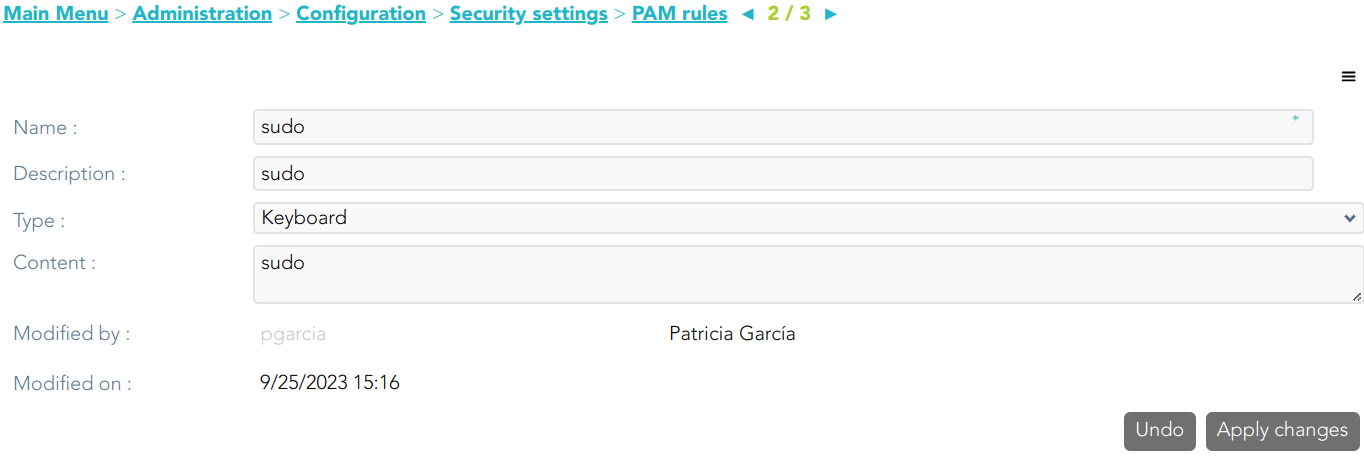](https://bookstack.soffid.com/uploads/images/gallery/2023-10/image-1696499194127.png) ##### Screen example [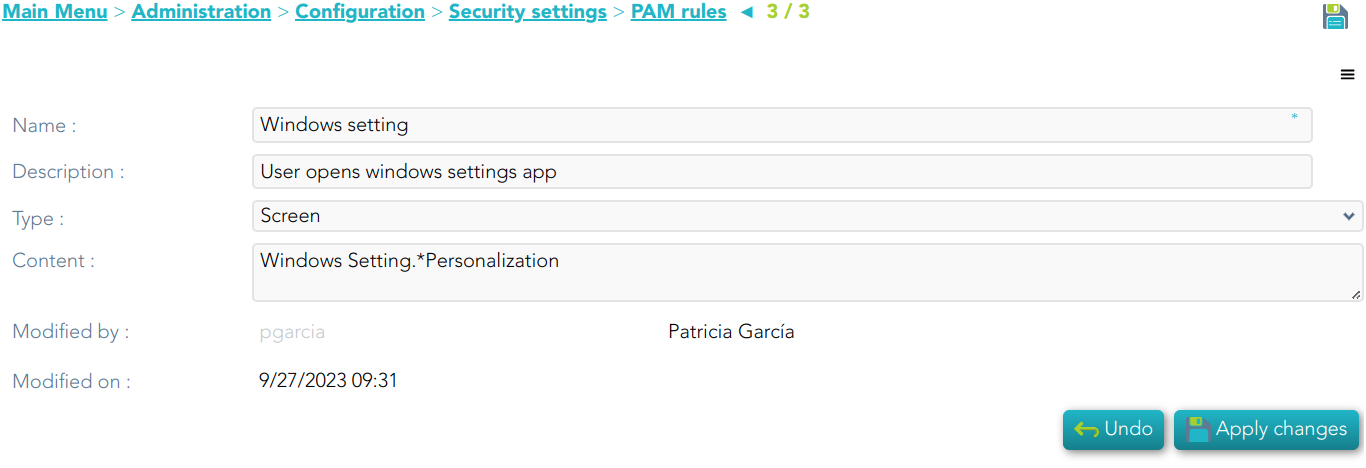](https://bookstack.soffid.com/uploads/images/gallery/2023-10/image-1696499256255.png) ##### Keyboard example [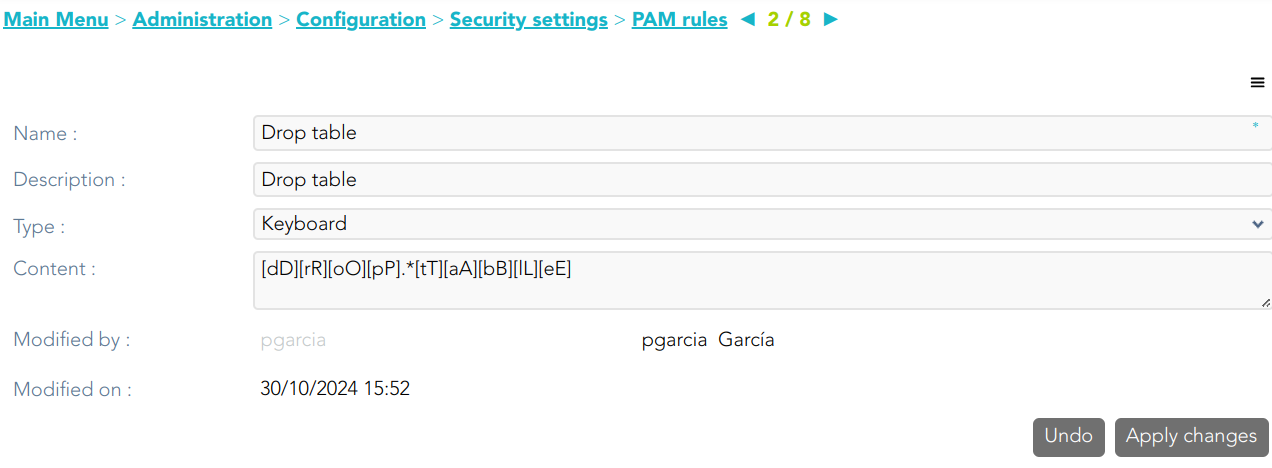](https://bookstack.soffid.com/uploads/images/gallery/2024-10/2evoPby06NumLhHs-image.png) ## Standard attributes - **Name**: name to identify the rule. - **Description**: a brief description of the rule. - **Type**: rule type. - **Keyboard**: Indicate the command typed in the terminal that you want to control. - **Screen**: Indicate the text displayed in the screen that you want to control. - **Content**: the content of the rule that Soffid will detect. Be in mind, that Soffid will consider blanks, returns, and all characters you type. - **Modified by**: user who modified that rule. - **Modified on**: the date and time of the update. ## Actions #### PAM rules query| **Query** | Allows you to query PAM rules through different search systems, [Quick, Basic and Advanced](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/search-types "Search Types"). |
| **Add or remove columns** | Allows you to show and hide columns in the table. |
| **Add new** | Allows you to create a new PAM rule. You can choose that option on the hamburger menu or click the add button (+). To add a new PAM rule it will be mandatory to fill in the required fields. |
| **Delete** | Allows you to remove one or more PAM rules by selecting one or more records and next clicking the button with the subtraction symbol (-). To perform that action, Soffid will ask you for confirmation, you could confirm or cancel the operation. |
| **Import** | Allows you to upload a CSV file with the PAM rules list to add or update PAM rules to Soffid. First, you need to pick up a CSV file, that CSV has to contain a specific configuration. Then you need to check the content to be loaded, it is allowed to choose if you want or not to load a specific attribute. And finally, you need to select the mappings for each column of the CSV file to import the data correctly and click the Import button. |
| **Download CSV file** | Allows you to download a CSV file with the PAM rules information. |
| **Apply changes** | Allows you to create a new configuration PAM rule or to update an existing one. To save the data it will be mandatory to fill in the required fields. |
| **Undo** | Allows you to quit without applying any changes made. |
| **Delete** | Allows you to delete a PAM rule. To perform that action, Soffid will ask you for confirmation, you could confirm or cancel the operation. |
(\*) You can visit the following page for more information about the issues: [https://bookstack.soffid.com/books/soffid-3-reference-guide/page/issue-policies ](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/issue-policies)and [https://bookstack.soffid.com/link/1153#bkmrk-pam-violation](https://bookstack.soffid.com/link/1153#bkmrk-pam-violation)
The PAM policies configuration is sent to the user-console.policies to the Store container. You can find this file at /opt/soffid/tomee/data/ips
| **Query** | Allows you to query PAM policies through different search systems, [Quick, Basic and Advanced](https://bookstack.soffid.com/books/soffid-3-reference-guide/page/search-types "Search Types"). |
| **Add or remove columns** | Allows you to show and hide columns in the table. |
| **Add new** | Allows you to create a new PAM policy. You can choose that option on the hamburger menu or click the add button (+). To add a new PAM policy it will be mandatory to fill in the required fields. |
| **Delete** | Allows you to remove one or more PAM policies by selecting one or more records and next clicking the button with the subtraction symbol (-). To perform that action, Soffid will ask you for confirmation, you could confirm or cancel the operation. |
| **Import** | Allows you to upload a CSV file with the PAM policies list to add or update PAM policies to Soffid. First, you need to pick up a CSV file, that CSV has to contain a specific configuration. Then you need to check the content to be loaded, it is allowed to choose if you want or not to load a specific attribute. Finally, you need to select the mappings for each column of the CSV file to import the data correctly and click the Import button. |
| **Download CSV file** | Allows you to download a CSV file with the PAM policies information. |
| **Apply changes** | Allows you to create a new configuration PAM policy or to update an existing one. To save the data it will be mandatory to fill in the required fields. |
| **Undo** | Allows you to quit without applying any changes made. |
| **Delete** | Allows you to delete a PAM policy. To perform that action, Soffid will ask you for confirmation, you could confirm or cancel the operation. |