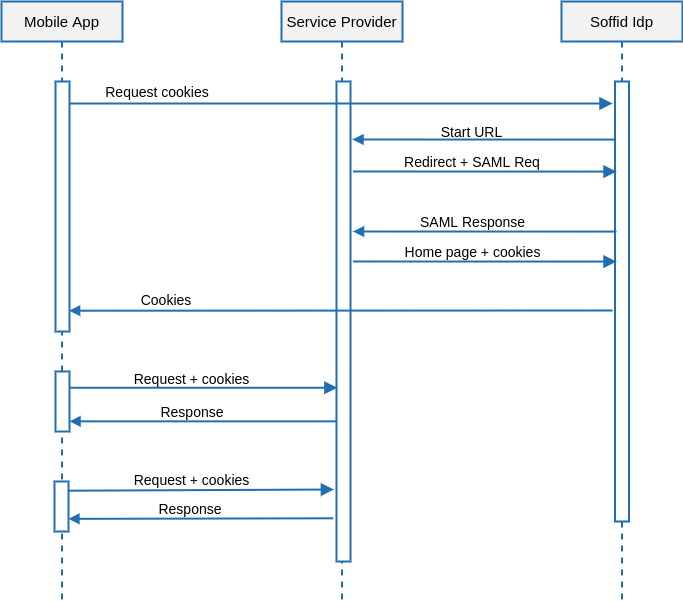
| POST [https://<YOUR\_SERVER>:2443/](https://soffid.bubu.lab:2443/token)userinfo/impersonate?url=http://targetapplication/ Accept: application/json Content-type: application/x-www-form-urlencoded Authorization: Basic dGVzdDp0ZXN0 \[ { "path":"/", "domain":"samltest.id", "name":"\_shibsession\_64656661756c7468747470733a2f2f73616d6c746573742e69642f73616d6c2f7370", "value":"\_fa49874951dd05c18a0f68642c0736e9" }, { "path":"/", "domain":"samltest.id", "name":"\_opensaml\_req\_ss%3Amem%3A88b0af3e1ff47c911257490bc1a5749dfda1670948a563cec2fdf9e8a799f2c4", "value":"" } \] |
| \[ { "path":"/", "domain":"samltest.id", "name":"\_shibsession\_64656661756c7468747470733a2f2f73616d6c746573742e69642f73616d6c2f7370", "value":"\_fa49874951dd05c18a0f68642c0736e9" }, { "path":"/", "domain":"samltest.id", "name":"\_opensaml\_req\_ss%3Amem%3A88b0af3e1ff47c911257490bc1a5749dfda1670948a563cec2fdf9e8a799f2c4", "value":"" } \] |
| POST [https://targetapplication/api/service1](https://targetapplication/api/service1) Accept: application/json Content-type: application/json Cookie: cookie1=value1 |
As security measures, the impersonation profile must be enabled, and the source application must be entitled to use it against the target application